Your Digital Fortress
Our Constant Vigil
Round-the-clock protection, proactive threat hunting, and swift response to safeguard your digital assets.
Your Trusted MDR friend
Monitor
- 24x7 MDR
- Proactive Threat Hunting
- AI enabled SOC
Respond
- Emergency Response
- Comprehensive Root Cause Analysis
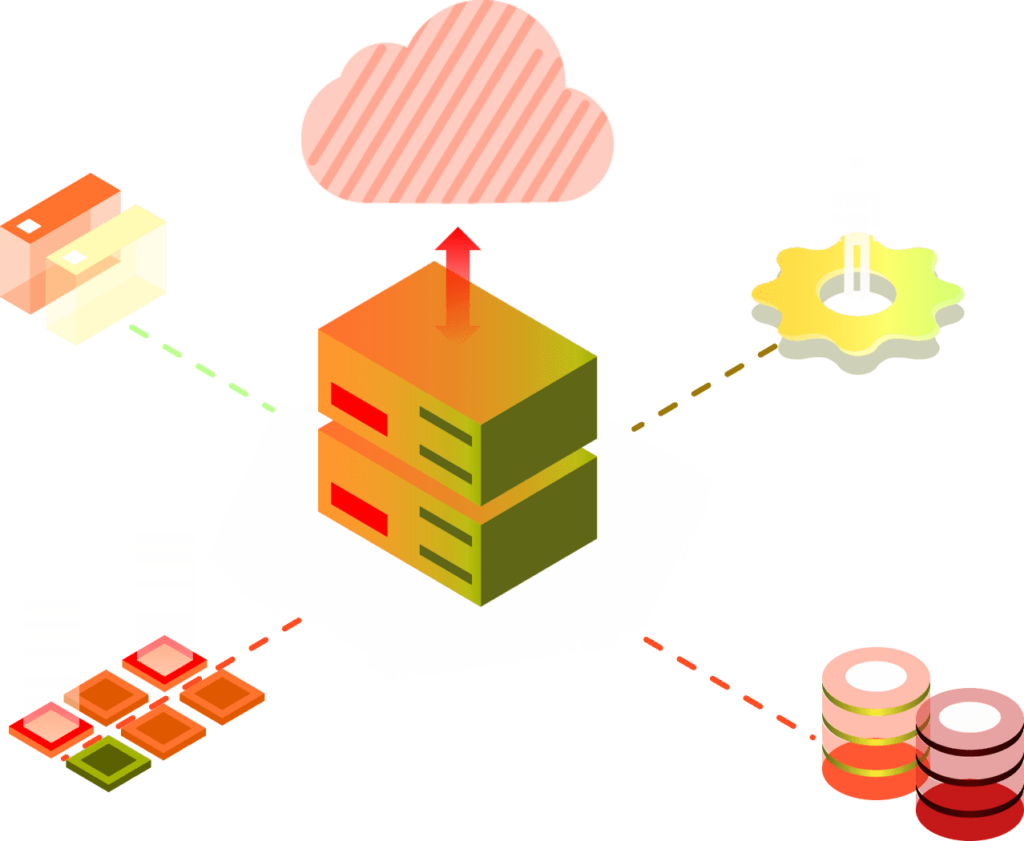
Threat Intelligence Feeds
Remediate
- Breach Mitigation
- Threat Modeling
- Automated Remediation
Recover
- Build Resilience
- Security ROI
- Operational Restoration
Core Features
SOC & SIEM Platform Engineering
- SIEM design and deployment
- Logs Normalization & Co-relation
- Log Analysis & Retention
- SOAR orchestration
- Parser development & API integration
- Log source and event flow tuning
Managed Security Operations Services
- 24x7 Real-time security monitoring
- Shared-Hybrid-Dedicated Models
- Alert Monitoring (Human + AI)
- Triage, containment, and recovery
- Incident Response & Management
- Governance & Analytical Reports
Threat Intelligence & Hunting
- Threat feeds ingestion
- Threat hunting & Attack discovery
- Recon, scanning, and enumeration
- Analysis and confirmation
- IoC enrichment
- Response coordination
24x7 Monitoring
Our 24×7 MDR service provides continuous, around-the-clock monitoring and management of your organization’s cybersecurity posture.
By leveraging advanced technologies and threat intelligence, we detect and respond to threats in real-time.
Our dedicated team of security experts analyzes alerts, investigates incidents, and takes proactive measures to mitigate risks. We offer rapid incident response, containment, and remediation to minimize impact.
Gain peace of mind knowing your systems are protected against evolving cyber threats, ensuring business continuity and data security.
Threat Hunting
Our Threat Hunting service involves proactively searching for cyber threats within your network and systems.
Utilizing advanced analytics, threat intelligence, and expert knowledge, we identify hidden threats and potential vulnerabilities before they cause harm.
Our team conducts thorough investigations to detect indicators of compromise, uncovering sophisticated attacks that may bypass automated defenses. By continuously monitoring and analyzing suspicious activities, we can swiftly respond to emerging threats.
Threat hunting enhances your organization’s security posture, providing deeper insights into potential risks and improving overall defense mechanisms.
Trust our proactive approach to safeguard your critical assets and maintain robust cybersecurity resilience.
Breach Response
Our Breach Management service provides comprehensive support during and after a security breach. We rapidly assess the situation to identify the scope and impact of the breach.
Our team contains and mitigates the threat to prevent further damage, while also conducting a detailed forensic analysis to determine the breach’s origin and method.
We assist in communication and compliance with regulatory requirements, ensuring timely reporting and transparency.
Post-breach, we help restore affected systems, recover data, and implement improved security measures.
Our goal is to minimize disruption, reduce risk, and enhance your organization’s overall security posture following a breach.
Security ROI
Our service helps you:
- Quantify the value of your cybersecurity investments
- Analyze the effectiveness of your security measures
- Calculate cost savings from preventing potential breaches
- Minimize downtime.
Our platforms detailed reports, showcases the financial and strategic advantages of robust cybersecurity.
With our insights, you can:
- make informed decisions
- optimize your security budget
- demonstrate tangible benefits of your cybersecurity initiatives to stakeholders
- maintain long-term protection and business resilience.
Technology Partners & Expertise















